Commit
This commit does not belong to any branch on this repository, and may belong to a fork outside of the repository.
fix(ecs): unnecessary CloudWatch logs ResourcePolicy (#28495)
This PR modified to avoid creating unnecessary `ResourcePolicy` in CloudWatch Logs. ## issue summary The related issue reports an error when using the awslogs driver on ECS. This error is caused by the creation of a ResourcePolicy in CloudWatch Logs that reaches the maximum number of ResourcePolicies. https://docs.aws.amazon.com/AmazonCloudWatch/latest/logs/cloudwatch_limits_cwl.html ## Current behavior In some cases, this ResourcePolicy will be created and in other cases it will not be created. Currently, `Grant.addToPrincipalOrResource` is used to grant permissions to ExecutionRole and Log Group in the ECS taskDef. https://github.com/aws/aws-cdk/blob/607dccb0fd920d25f0fe2613b83c9830322c439e/packages/aws-cdk-lib/aws-ecs/lib/log-drivers/aws-log-driver.ts#L138 https://github.com/aws/aws-cdk/blob/607dccb0fd920d25f0fe2613b83c9830322c439e/packages/aws-cdk-lib/aws-logs/lib/log-group.ts#L194 https://github.com/aws/aws-cdk/blob/607dccb0fd920d25f0fe2613b83c9830322c439e/packages/aws-cdk-lib/aws-iam/lib/grant.ts#L122 `Grant.addToPrincipalOrResource` first grants permissions to the Grantee (ExecutionRole) and creates a resource base policy for cross account access in cases where certain conditions are not met. This condition is determined by the contents of the `principalAccount` of the ExecutionRole and the accountID in the `env.account` and whether or not these are Tokens, but in this scenario, cross account access is not necessary. https://github.com/aws/aws-cdk/blob/607dccb0fd920d25f0fe2613b83c9830322c439e/packages/aws-cdk-lib/aws-iam/lib/grant.ts#L141 Also, when the `LogGroup.grantWrite` call was added to `aws-log-driver.ts`, the ResourcePolicy for logs could not be created from CFn and only granted to the ExecutionRole. #1291 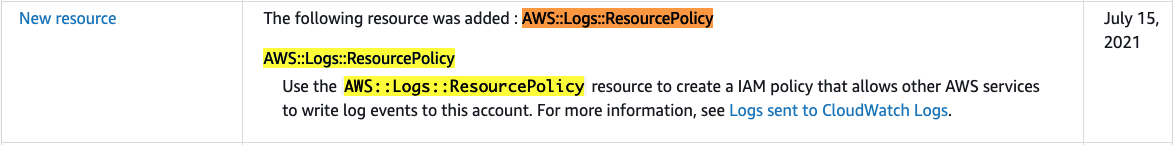 https://docs.aws.amazon.com/AWSCloudFormation/latest/UserGuide/ReleaseHistory.html Therefore, the resource base policy should not be necessary when using the awslogs driver. ## Major changes This PR changed to grant permissions only to ExecutionRole when using the awslogs driver. With this fix, ResourcePolicy will no longer be created when using the awslogs driver. I don't consider this a breaking change, as it changes the content of the generated template, but does not change the behavior of forwarding logs to CloudWatch Logs. However, if this is a breaking change, I think it is necessary to use the feature flag. fixes #22307, fixes #20313 ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
- Loading branch information