-
-
Notifications
You must be signed in to change notification settings - Fork 3.9k
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
proxy: Add header and uri load balancing policies #1463
Comments
|
Anyone can propose a new policy. The requirement really is adding the implementation here https://github.com/mholt/caddy/blob/master/caddyhttp/proxy/policy.go#L21-L24. |
|
Caddy already supports round robin, least conn, and source (IP hash). I think implementing |
|
Hey, i would implement these feature. But i've a question. Where do we want to get the number of "firsts" machine? I think we could make it in a static way, or about questioning an url for it. Greetings. |
|
@pbeckmann Good question... I'm not sure how haproxy decides that. Anyone know? |
|
I looked in the documentation of haproxy and found
Source: http://cbonte.github.io/haproxy-dconv/1.8/configuration.html#4.2-balance So it's seems pretty easy. I'll look now into the testing and send you then a pull request :) Greetings |
|
I would lovely implement hdr and and uri too.
Anyway, first @mholt should decide, whether this could be useful, or does we wait for a issue and close this one? |
|
@pbeckmann We can add another argument to policy for the header (don't call it hdr) policy, sure. Let me give you collaborator status so you can push your changes to a branch instead of a fork, and help review pull requests from others, etc. |
|
I would like to see this implemented in Caddy: http://blog.haproxy.com/2013/04/22/client-ip-persistence-or-source-ip-hash-load-balancing |
|
What exactly do you mean with "this"? The ip hash algorithm already exists in caddy. |
|
It's not clear from this issue what exactly how |
|
@mholt I use caddy like this: one caddy -> two varnishs (HTTP Cache Server, usually based on uri).
Please support |
|
@vicanso Sure, but is |
|
@mholt Yes. |
|
Fair enough -- somebody who is new to this project or new to Go can add the How exactly does |
|
I'll have a look at URI policy. I'm thinking simple version to start with, and then extend with length and depth settings. Sounds OK? |
|
@pbeckmann @cez81 No, it's fine -- go ahead, these are small and modular components that I can copy over to the new proxy middleware. I'm not too far into it yet. |
|
Cookies are also common for session affinity, but Caddy currently wouldn't be able to support that method without imposing a globally defined (or even hard-coded 😨 ) cookie name. I think the I think an ideal solution would be to slightly change the way the Example: The existing function signatures would need minimally updated, e.g. but that would also allow for and The existing |
|
@zikes Great idea; Sounds like a good plan to me, although maybe we should limit it to just one string argument passed into the policy maker. |
|
I gave the Header policy a go at #1751. I would also like to implement Cookie, but I ran into some difficulties with that. In the nginx implementation, if the cookie is not present then nginx will generate the cookie and return it on the response. Unfortunately the response is currently not available in the A somewhat inconvenient alternative would be to create the cookie outside of the proxy policy, in the Caddyfile, so that it is available before the policy is evaluated (a Having the cookie (or at least the cookie's value) generated and available prior to the policy being evaluated is important, otherwise the policy may route to a different host on subsequent requests. |
|
I would like to try this out either if no one against this:) |
|
Go for it, no one else is working on it! |
|
@mholt I looked at code and cookie policy can be implemented similiar to header policy(with hashing of value) and it's pretty easy task(actually i already write the sample code, need to test it so...). But reading comments to this issue i found out that you are expecting some additional properties/behaviour for this policy, right? So how should i do this? With simple hashing(we expect that our upstream server sets cookie for user)? Or we want to set cookie from caddy to user? Or somehow mixed of this two? |
|
@SmilingNavern I'm not sure, since I'm not using this feature. Maybe someone else in this thread with an interest in this feature can give you some feedback. |
|
@jonesnc could you please elaborate on the cookie feature? What do you like to see in this feature? |
|
@mholt I was thinking about this issue. Part of the problem that if we use hash of cookie to route to specific upstream, than we need somehow to deal with initial empty request which gets cookie. And that initial request should be sticky to this upstream. I believe that haproxy/nginx solve this problem with setting cookie to client(this is not possible with current policy implementation). I will look into source code of haproxy, but maybe you have some thoughts on this. |
|
I would like to see Caddy implement the same behavior that HAProxy offers. In my particular use-case, I proxy a web application with 3 nodes, and when I log in to one of those nodes a cookie gets created (JSESSIONID). So, I want Caddy to load balance based on 1) least connections if JSESSIONID is not set, and 2) if JSESSIONID is set, proxy to the node that created the session (e.g., the node that included the SET-COOKIE HTTP header). Basically a typical cookie-based session persistence setup. More info on this behavior in haproxy can be found here: |
|
@jonesnc yea, thank you:) i already read this article. I understand what you want. Will try to propose some MVP solution and discuss with mholt about implementation. Currently the most hard part is setting cookie value from caddy policy. |
|
@SmilingNavern great! I'm glad there's someone smarter than me working on this feature 👍 |
|
@SmilingNavern @zikes The cookie header is usually only used to determine whether to access the site for the first time. It seems that there is no other use, so it seems that there is no problem in generating a standard cookie. |
|
@daiaji yeah, the main problem is to add possibility to modify user cookies within the policy plugin. Main problem is that you want cookie sticky sessions and you want that user which comes to your backend for the first time will be there second time. Client -> caddy -> backend1 |
Are you sure? Why would the hash change regardless of whether the cookie is set? The source IP will be the same regardless of cookies, no? |
|
Okay, maybe i missing something but here is how i see it. We want that new clients without cookie will go to any backend and then stick to this specific backend. If we just use hash of cookie following would happen:
In haproxy case they write backend number to cookie and parse it later. So it becomes really sticky to first chosen backend. I am not aware of another approaches or how to do it differently without loading caddy too much. If we want implement it in haproxy way then we need to access in policy plugin to write cookies. Or design something better) |
No, I mean use the However, if the client's IP changing during a session is a concern, and you don't want to re-auth in that case, then there's probably a not-hard way to add the ResponseWriter to the RegisterPolicy function so you can set cookies. |
|
I believe people who want sticky sessions with cookies want it for mobile devices which can change their mobile devices. Oh, okay. I would try out to add ResponseWriter to policy if that's okay with you |
|
@SmilingNavern @zikes The Header policy should increase the value of the http header. |
|
@daiaji sorry, but i didnt get your last point. What do you propose? What do you mean by "increase the value"? |
|
@SmilingNavern Http Header has value. Sorry, or should I modify the configuration file like this now? |
|
Policy is used only for balancing between multiple backends with preconfigured rules. So if you want to modify headers you should use something else. If i understood you correctly. This issue is about only balancing policies |
|
@SmilingNavern I don't need to modify the http header. I just want to determine the content of the http header and load balance. Can the |
|
@daiaji what do you expect? How do you want it to work? The current header policy implementation is based on hashing of header content. So you can use: and it will be load balanced based on hashed content of this header. Is this what you want? |
|
@SmilingNavern This is the problem, the header policy does not check the specific content of the http header. |
|
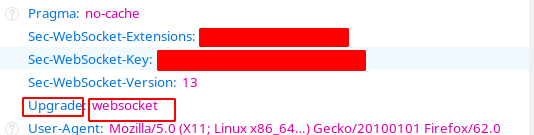
@daiaji If I'm understanding what you're asking, I don't think your case will work here, because If what you want is to only proxy based on some condition, then what you'll want to do is the following: Set a rewrite rule to change the path of a websocket connection to something special (as a placeholder), then proxy on that path, and strip the special string with the I posted a question about that in the forums a couple years ago: https://caddy.community/t/websocket-proxy-condition/512 |
|
@francislavoie I really hope this is done. |
|
At some point, #1948 will be completed, so you'll be able to use that. For now, what I wrote is probably your best option. I don't see more conditional logic being added to @SmilingNavern Just wondering, what's your status on the |
|
@francislavoie This is great! It's looking forward to it! |
|
@francislavoie i am at early stage on this) actually it would be good as a separate issue. |
|
Load balancing policies have been implemented into v2; closing. If new ones are needed, open a new issue or submit a PR! |
Can caddy support more load balancing algorithms such as haproxy.
round-robinfor short connections, pick each server in turnleastconnfor long connections, pick the least recently used of the serverswith the lowest connection count
sourcefor SSL farms or terminal serverfarms, the server directly depends on the client's source address
uriforHTTP caches, the server directly depends on the HTTP URI
hdrthe serverdirectly depends on the contents of a specific HTTP header field
firstfor short-lived virtual machines, all connections are packed on thesmallest possible subset of servers so that unused ones can be powered
down
The text was updated successfully, but these errors were encountered: